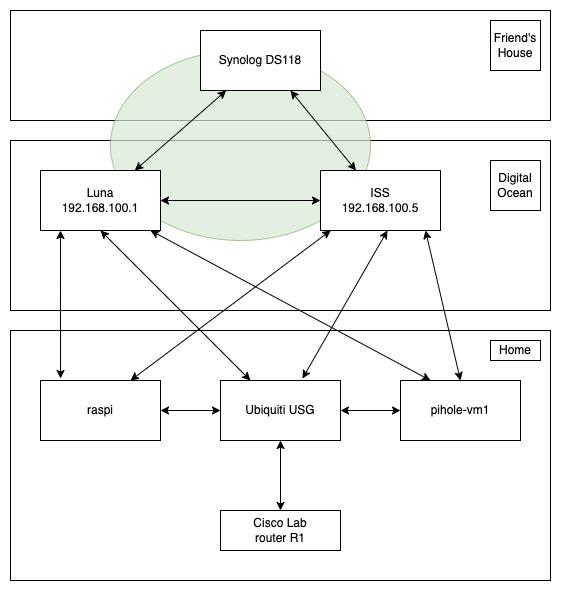
I have recently switched most of my offsite network connections to WireGuard, away from ZeroTier. This is great for all of my systems except for one: the NAS (a Synology DS118) I have at a friend's house for offsite backup. That NAS can run ZeroTier and WireGuard, but I don't know of any dynamic routing protocol options for it, so I can have only a single WireGuard connection rather than the two I want. My solution here is to create a ZeroTier network between that NAS and the two VMs I have at DigitalOcean. For my purposes, that is close enough to having two WireGuard links and the ability to route to both of them.
Another issue I wanted to resolve was the CPU load on my USG: with WireGuard running on the USG, high traffic utilization on the WireGurad links results in 100% CPU load on the USG, and that slows everything down. The solution there was to add WireGuard links from my Pi-Hole systems at home to my DigitalOcean VMs, and to increase the OSPF link cost from the USG to the DigitalOcean VMs. As long as my USG is up, I'll have connectivity to my DOVMs, but if one of my Pi-Hole systems is up, I will have better connectivity to the DOVMs.
I also wanted to set all of this up with redundant links and ECMP such that any link can be down, and have everything continue to work.
Below is a current network diagram. The offsite links are WireGuard with the exception of the ZeroTier network (shown in green) that connects the two DOVMs and the NAS. (The two DOVMs are of course also connected by a WireGuard link.) A single OSPF area is used throughout, for all of the routing.
This has been an enjoyable project, and a great learning experience.
Daniel's Blog
I am a system engineer in the Raleigh, NC area. My main interests are Unix, VMware, and networking. More about me, and how I got started.
Categories
Tags
- IC-7300 1
- T1 1
- ansible 2
- anycast 2
- atari 1
- autofs 1
- backup 2
- battery box 1
- bgp 1
- cables 2
- cisco 2
- dashcam 1
- digitalocean 2
- disney 1
- diy 6
- dkim 1
- dns 2
- docker 7
- dsm 1
- ecmp 1
- email 2
- encryption 1
- esp32 2
- esphome 2
- esxi 4
- f150 3
- freebsd 1
- frr 4
- ft7800r 3
- ftm400 1
- git 1
- ham radio 6
- hardware 2
- home assistant 4
- home automation 2
- home lab 1
- homelab 2
- icloud 1
- ipad 1
- iphone 1
- iscsi 1
- kasa 1
- letsencrypt 1
- m5stack 2
- m900 1
- mac 1
- macos 3
- mikrotik 1
- minfs 1
- mobile 1
- monitoring 1
- nas 1
- network 1
- networking 3
- nfs 3
- ospf 4
- pelican 1
- perl 1
- php 1
- pi-hole 2
- plex 1
- portainer 1
- postfix 5
- pota 1
- prepping 1
- printer 1
- pxe 2
- python 1
- r610 3
- rack 4
- radio box 1
- raspberry pi 9
- raspi 1
- routing 2
- rsync 1
- satellite 1
- scanner 3
- shell 4
- solenoid 1
- spf 1
- ssh 2
- ssl 2
- synology 9
- tinyminimicro 1
- traefik 2
- ubiquiti 6
- udm-se 1
- unix 8
- update 2
- usg 5
- virtualization 4
- vmware 4
- wireguard 6
- ysf 1
- zerotier 6